4 steps toward cloud security automation
Automating security in the cloud can be invaluable for threat detection and mitigation. Explore the four key areas where security professionals should implement automation.
In cloud environments, particularly IaaS clouds, security teams have a wealth of tools available to automate various security controls and operations. For many, it's difficult to know where to start. What makes the most sense to automate, and why? Every security team's needs will differ to some extent, but there are some well-known controls and processes that most teams can automate without disrupting operations.
Step 1. Configure containers
The first step for cloud security automation should be instance and container configuration management. As all instances and containers are software-based, with images that are defined in template formats, security teams can work to implement configuration hardening guidelines and standards in the images. Orchestration tools like Puppet, Chef, Ansible and SaltStack can then implement these standards automatically.
The additional benefit of using tools like these is that each configuration profile is also defined in a template that can be continuously reevaluated to account for changes as they occur. While these tools can be used effectively on premises, there are even more automation options in the cloud with integration opportunities between these platforms and cloud-native systems, like AWS OpsWorks, which offers managed instances of Puppet and Chef.
Step 2. Use infrastructure as code
Another common and practical step in automating cloud security operations and cloud environment configuration is the use of infrastructure as code. All major cloud providers support these templates either natively, such as in AWS CloudFormation, Azure Resource Manager or Google Cloud Deployment Manager, or through third-party platforms, like Terraform. With many environment and asset configurations defined in a template format, security teams can ensure smooth and consistent deployments, audit template files for adherence to standards and automate security configuration items along with infrastructure deployments.
This article is part of
What is cloud security management? Guide and best practices
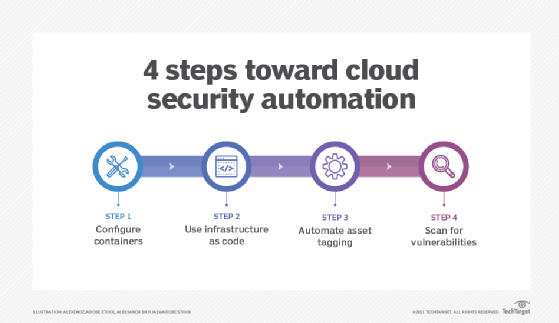
Step 3. Automate asset tagging
A third opportunity for automating security in the cloud is automated tagging of assets based on specific security conditions detected in the environment. One of the top advantages of the cloud is the ability to enable cloud control plane logging, which effectively logs everything in the environment and stores logs in a central location. Once services such as AWS CloudTrail, Azure Log Analytics, Azure Monitor and Google Cloud's operations suite, are enabled, security teams can build monitoring filters on top of them to detect suspicious activities or events.
These activities trigger serverless functions that tag running instances or even user accounts with metadata. Metadata is used to track assets and quickly discover possible investigation opportunities. Once assets are tagged, any number of automated or semi-automated security strategies can be pursued. Strategies include isolation of systems by changing their network access control policies, forensic evidence collection from the systems, system suspension or termination, or disabling user accounts.
Step 4. Scan for vulnerabilities
A final area where cloud security automation makes sense is vulnerability scanning. All major network and application vulnerability scanners have adapted to function in major cloud environments and are often able to integrate with cloud provider APIs to enable continuous scanning and monitoring of assets in the environment. When new assets appear, event monitoring and alerting trigger automated scans.
Integration of agents into system images can also lead to automated reporting and even policy application with some tools. Once the environment is up and running with defined service configurations, use cloud-native tools, such as AWS Config or Capital One's Cloud Custodian, to automate the assessment and maintenance of configuration for the cloud environment itself.
Through defined rules and policies, these tools can check to see whether S3 buckets have been made public, for example, and then change the settings back to a desired state. Through cloud security automation, both assets and the environments themselves can be assessed and remediated continuously.







