How to develop a cloud backup ransomware protection strategy
Deploying cloud backups for ransomware protection has become a common security strategy. Here's how to properly vet cloud storage vendors to ensure backups stay secure.
The increasing rate of threats incorporating ransomware and data-specific attacks is prompting many organizations to implement a new data backup and recovery model that includes cloud-based storage.
Most mature enterprises have several tiers of backups and replicated data for business continuity and disaster recovery (BCDR) purposes. But the specter of ransomware is driving some organizations to consider isolated backups. These are backups that aren't reachable or accessible from the core corporate environment without making infrastructure changes and/or requiring numerous administrative authentication/authorization adjustments.
Common tactics for cloud backup ransomware protection include the following:
- Building a new network segment within the organization's environment for these backups, with a "deny all" firewall protecting the segment -- these rules are only relaxed when the data is needed or for replication.
- Creating a new, isolated cloud-based backup using both on-premises and cloud-based network restrictions similar to those just mentioned -- alternately, this isolated backup could be in a secondary or backup data center.
- Requiring multiple administrators to collaboratively enter credentials and multifactor authentication information.
Getting started: Developing a cloud backup strategy
To develop a cloud backup ransomware protection strategy, the following distinct areas of the organization should be involved in the planning phase:
- IT operations. IT operations teams should look at the types of data to back up and how long the data should be stored.
- BCDR planning. For BCDR planning teams, the data should be aligned to standard metrics, such as mean time to recovery, recovery time objective, recovery point objective and others.
- Information security. The sensitivity of the data stored and replicated is critically important. As a result, security teams should focus not only on the types of data backed up, but security controls available in the cloud to help protect this data.
- Legal and compliance. Any required legal and regulatory needs should be addressed early to make sure all storage and archival requirements meet industry and best practices requirements.
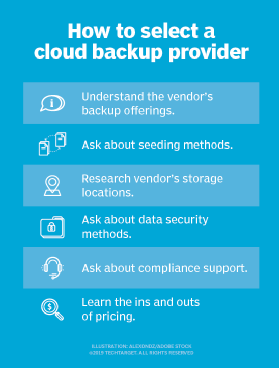
Data security questions to ask cloud storage providers
Organizations should ask their cloud storage providers a series of questions that covers everything from data center security to storage architecture and network security, storage management and security processes.
This article is part of
What is ransomware? How it works and how to remove it
Data center security
Initial questions should center on the physical security of a vendor's data centers and the personnel who operate systems and applications within those environments. These questions include the following:
- Is physical access to the data center restricted? Which security methods are required for access -- for example, biometric retina scanners? Enterprises should expect providers to maintain strong physical access controls at these facilities.
- Is the data center staffed and monitored 24/7? If so, how are shift changes handled?
- Does the data center have video surveillance and audit logs tracking visitors and their times of entry and exit? How is video surveillance monitored?
- Are background checks performed on employees with physical or managerial access to the infrastructure? What type of checks are performed, and how often?
- Are there intrusion alerts, and is there a documented response plan in case of a breach of physical security at the data centers?
Storage architecture and network security
Organizations must be cognizant of the general security design considerations in place in the cloud provider environment. These controls are considered fundamental security program elements that any mature program should support. Consider the following criteria:
- What authentication methods are required for users when accessing storage components and areas? In particular, a provider's storage administrators should have strong authentication requirements.
- Are there secure configurations that mandate default password changes as part of the installation process? Secure configurations should deny any and all services, features and functions unless users specifically activate them, providing a default deny stance for all configuration controls.
- What types of security event monitoring and logging are in use? Any platforms and applications must provide the ability to detect security events and log them accordingly. Users should have the ability to send security alerts to management consoles, element managers, pagers, email and other sources. In many cases, this data is only available to cloud provider teams, but users should be aware of what technologies and processes are in place.
- How is multi-tenancy deployed, and what technologies are used to segment and isolate different tenants' data? Virtual firewalls, hypervisors, storage area network (SAN) isolation tools and techniques, and network segmentation are all viable options. Cloud providers should be willing to disclose what they use to protect data on shared platforms.
- Are network device user permissions and passwords audited, and how often? Cloud providers should periodically review user permissions and passwords to ensure they remain valid and up to date.
- Are systems servicing each customer segregated from other network zones, both logically and physically? There should be separate firewalled zones for internet access, production databases, development and staging areas, and internal applications and components.
Storage access and management security
Managing access controls and session security for access to the storage environment should be of paramount concern for both cloud provider administrators and enterprise users. To defend against common security threats, such as ransomware, cloud storage should be assessed based on the following criteria:
- Do management tools and other administrative applications store user passwords in an encrypted format? If so, what type, and is this encryption tested regularly? Also, does the storage management application enable configuration and enforcement of password length, type and duration?
- What types of secure connectivity are permitted to the cloud storage infrastructure? Are more secure communications protocols, such as Secure Sockets Layer/Transport Layer Security or Secure Shell, supported?
- Is there an active user session timeout?
- Do the management tools support multiple administrator profiles to provide granular security levels? Administrative applications for accessing and configuring cloud storage should have configuration options that restrict administrator access based upon time, day, function and other attributes. All administrator action should be logged for auditing and alerting, and logs should be available to enterprise security teams.
- Can the cloud storage management application define granular roles and privileges? To maintain proper separation of duties and enforce the principle of least privilege, this capability should be considered mandatory.
Security processes
The majority of the focus on security-oriented processes within a cloud storage provider should be on software testing and development security, as well as patching and vulnerability management.
Questions to ask include the following:
- Does the cloud storage provider test hardware and software in fully secured and patched configurations to assess the vulnerability of the servers, networks and applications?
- Is a process in place at the provider to track and report security vulnerabilities discovered within the cloud storage products? The provider should also delineate between general announcements and contact methods for particular customers as a part of its incident response processes.
- What notification and escalation procedures are followed if security breaches or other potentially serious security incidents are encountered?
- Is there an established and documented process for the distribution of critical software patches and noncritical security updates internally?
- Is there an established process for testing security in the development and quality assurance cycles? This should include scanning source code for top issues -- among them the Open Web Application Security Project Top 10, buffer overflows, poor authentication and session handling.
Cloud-based storage supplements data backup strategies already employed by mature organizations. Those strategies include on-premises standard backups using tape or disk or large-scale replication of virtual data contents with SAN/network-attached storage integration, as well as secondary backups using tape or disk sent to an off-premises backup provider. Finally, for newer scenarios, such as ransomware concerns, short-term isolated backups for end-user content and/or core data center critical assets can be considered.






